


By: Joe OsbornJune 20, 2020
More than 3 million Americans reported being victims of fraud and identity theft in 2019. Consumer data and information is not only being stolen and used for illegal activities but it is also being shared with unauthorized parties and companies for advertising purposes. Whether it’s Facebook giving personal user data access to Cambridge Analytica or Equifax exposing personal information of 147 million users, consumers can no longer rely on companies and websites to keep their personal data and information safe.
Identity theft in the United States experienced a huge jump in 2019, increasing by ~50% from 2018 numbers. As COVID-19 affects millions of people financially and desperation sets in, 2020 might be even worse.
While identity theft could happen to almost anyone, those in the 20-29 age group reported it most and accounted for ~33% of all identity theft cases. However, people over 70 reported much greater median losses than those in other demographic segments.
The 2019 data also shows that among all identity theft reports, credit card fraud remains the most common type of identity theft, representing a whopping 88% increase year over year and accounting for 271,823 of reported cases.
Other common types of identity theft include loans, utilities, tax and bank fraud.
As eCommerce and online shopping continue to overtake retail, cyber crime will not stay far behind. By the year 2021, more than 2.14 billion people are expected to purchase goods and services online (Source)
Despite having improved security standards, most online platforms are still vulnerable to cyber attacks that seek to extract personal user information. Add COVID-19 to the mix and you have the perfect environment for cyber attacks and data breaches to take advantage of unaware consumers. (Source)
Before you do anything online, it’s vital to ensure that you are protecting yourself and your personal information at all cost. Whether it’s your device, your internet network or even your browser, you must take the necessary precautions to ensure your private information and data is secure.
This guide covers multiple security aspects and you can skip to any section by clicking one of the buttons below:

The most crucial type of information you need to keep private is your personally identifiable information (PII).
The term “PII,” as described in OMB Memorandum M-07-1616 is information that can be used to trace or distinguish someone’s identity, either alone or when combined with other PII. These include:
Your full name, maiden name, mother’s maiden name, etc.
Your registered email, mailing address and residence address.
Your driver’s license number, social security number, passport number, taxpayer ID number, etc.
Your dedicated IP or MAC addresses tied to your user account.
Your personal cell, home or work numbers.
Your car's ID or title numbers
Remember to reveal only what is necessary to complete a purchase or registration process. Some websites will ask for your Facebook or Instagram accounts for sharing purposes, which is often not mandatory. Your personal information can be accessed through third party logins.
A lot of retailers try to obtain additional details like favorite sports, types of entertainment you prefer, annual household income, etc. These are mostly used for personalizing advertising and increasing conversions for companies. We recommend not adding any information that is not required and registering/logging in through an email address.
The most important information that you should NEVER share are your government issued ID’s and bank related information outside of credit cards/debit cards used for purchases. These include:
It’s important to reiterate the point of only sharing the information you absolutely have to in order to register on a website or complete a purchase. We strongly recommend disclosing as little Personally Identifiable Information as possible.
In a lot of cases, you don’t need to disclose your actual birth date to complete a purchase or sign up for a service. Your birth date is an extremely important piece of information that if comprised, can easily be used for fraud and identity theft purposes. (Source)
Your address is also very important but if you are making any sort of purchase that requires delivery, you have no alternative other than a PO box. But, refrain from disclosing your actual address in all cases where it’s not required.
Here some data sharing policies to look for when signing up and disclosing your personal information on a website/app:

Since July 2019, more than 79 percent of smartphone users have made a purchase online using their mobile. Chances are you’ll most likely be using your smartphone to shop online as well. Here are some tips to consider:
Use a pass code, fingerprint, face recognition, or pattern — depending upon your phone’s capabilities to keep it locked and protected. Also, keep “Find My Device” activated on your device to prevent data theft if stolen.
Your phone’s operating system requires frequent updates to protect against malicious attacks and enhance your security. To make sure the OS is up-to-date by navigating to About Phone > General > System/Software Updates.
Avoid using public Wi-Fi and rely on data services. Use a paid VPN tool if you're using public Wi-FI to ensure that your connection is secure. Note that free VPN services can leak your private data.
Unless you know what you’re doing, we recommend that you not jailbreak your phone. It may seem tempting to use a particular app that requires jail breaking, but this could put you at high risk.
Cybercriminals develop rogue mobile apps to collect user data. Torrenting or downloading songs illegally can further expose you to malicious files.
Services like Norton and McAfee will give you cross platform protection against malware, viruses, and hackers.
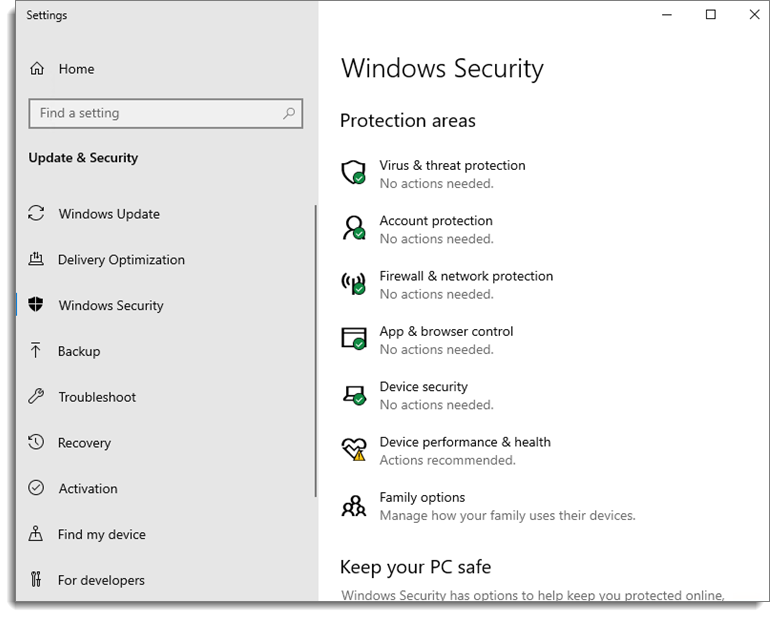
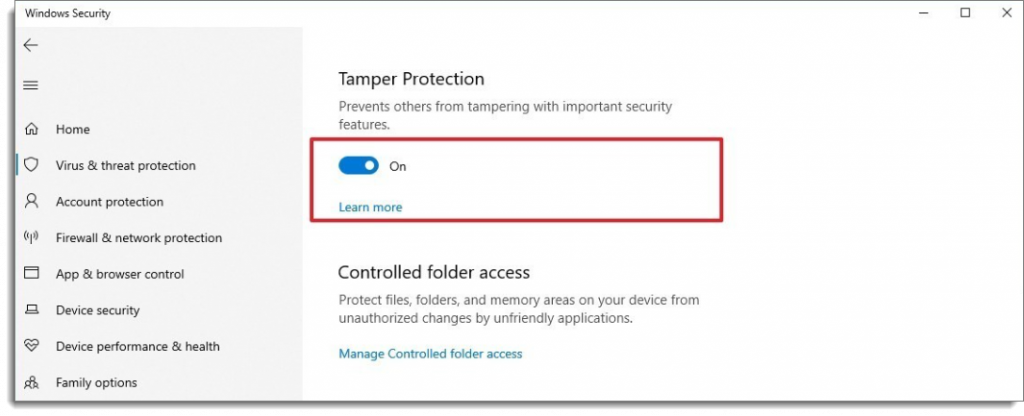
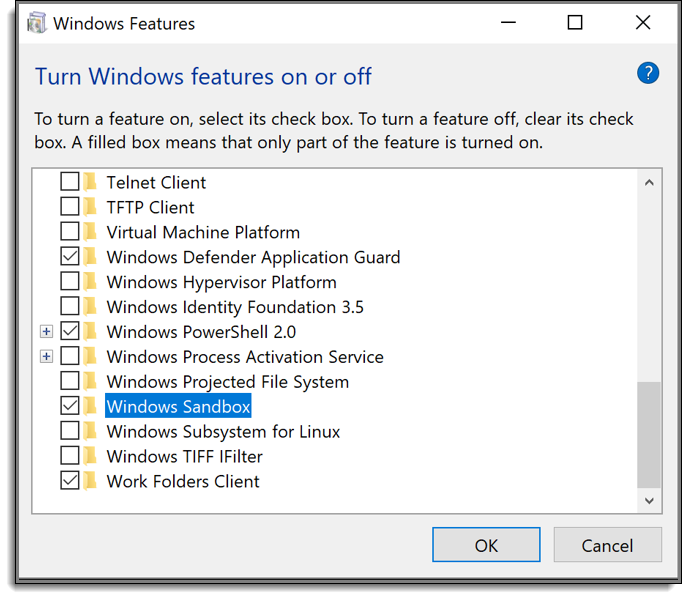
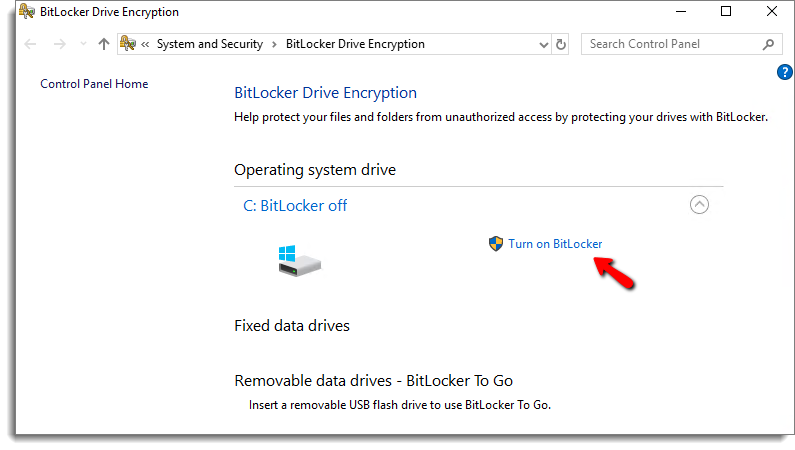
Similar to mobile, you must take precautions against common computer viruses and cyber threats. Here are some basic tips:
Most consumers use Windows and Mac OS to perform their daily tasks. Since Linux is more on the tech-savvy side, we’re not going to include any Linux server protection tips in the following section. Here are some Operating System specific tips to keep your device protected at all times.
Bonjour lets you connect to your local area network. However, if the network isn’t trusted, consider disabling it by using this command in the terminal:
sudo defaults write /System/Library/LaunchDaemons/com.apple.mDNSResponder ProgramArguments -array-add “-NoMulticastAdvertisements”
Similarly, the following command will enable Bonjour:
sudo defaults write /System/Library/LaunchDaemons/com.apple.mDNSResponder ProgramArguments -array “/usr/sbin/mDNSResponder” “-launchd”
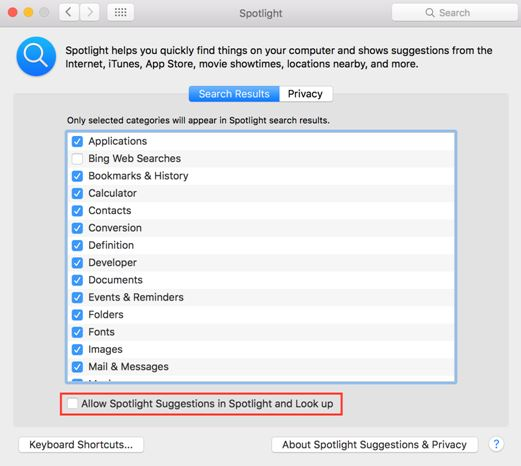
Disable Spotlight Localization:
Spotlight helps you find information stored in your hard drive, as well as on the web. However, it also requires your location to perform the task and sends the information to a remote service. It exposes you to additional security risks and we recommend keeping this function disabled.
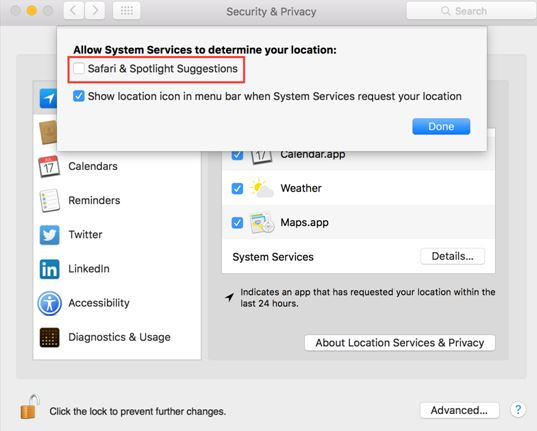
Navigate to System Preferences > Security & Privacy > Privacy > Location Services. Now, open “Security & Privacy,” find “Details,”and uncheck “Safari & Spotlight Suggestions.”
To disable Spotlight Suggestions, navigate to System Preferences > Spotlight and uncheck “Allow Spotlight Suggestions in Spotlight and Look Up.”
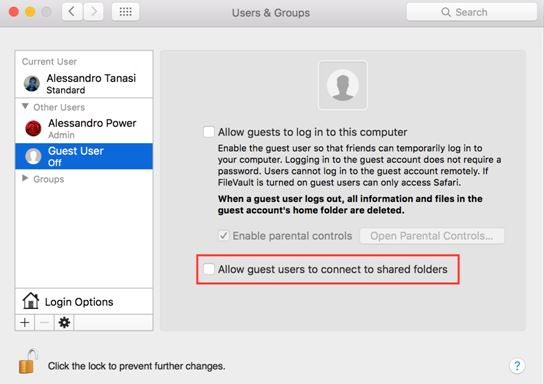
Navigate to System Preferences > Users & Groups > Guest User and uncheck “Allow guests to log in to this computer” to prevent others from messing up your sensitive data.
Navigate to System Preferences > Security & Privacy > Advertising and check “Limit Ad Tracking” to opt out of receiving targeted ads.
Email is another vulnerability point that hackers and scammers can easily attack. While many email clients have significantly enhanced their security features over the last decade to prevent fraud and scam related emails ever reaching your inbox, threats still exist within any email client.
Here are some security tips that you should consider whenever using your email client:
It's a good practice to have at least a few email accounts to reduce your risk in case of a breach. You should have separate email accounts for work, friends and family and shopping.
Any email requesting your personal information such as password recovery, profile update or any other login information should be deleted. Typically they will impersonate high profile sites.
You should have a reputable anti virus and malware software installed on your device that scans all emails for vulnerability threats.
Don't open attachments from unknown parties. These attachments typically come in PDF, Word or Excel formats and have malicious software.
Public WiFi networks can expose your login information through network sniffers whenever you check your email. Avoid checking your email when using a public wifi network.
If you receive an email with external links, make sure you check where the link is pointing to by hovering your mouse over it. Some links may redirect you to malicious websites.

Setting up a robust home network is challenging. However, optimizing the web connectivity of your devices, as well as protecting your sensitive data is well worth the extra work. The following tips will help you build a stronger home network.
Usually, new routers are given a default Service Set Identifier (SSID) name and password. Change this information immediately after connecting to the Internet for the first time. Depending on which manufacturer designed your router, hackers can guess the default SSID and password easily, if not changed right away.
Based on your ISP and router, you might get to decide how your Wi-Fi network will be encrypted. As you are setting up the router for the first time, you’ll find several options regarding how to encrypt the network. For enhanced security, consider choosing WPA2-AES. It can protect your network against force attacks seamlessly.
Most routers are usually dual-band, which means they are able to broadcast both 2.4 GHz and 5 GHz bands as per their signal. Consider getting the 2.4 GHz band if your house is too big and requires Wi-Fi to transmit across several floors and or walls. You can also use the 5 GHz band for better protection and faster speeds. Experts, however, recommend experimenting with both to see which suits your needs the best.
Always keep the software of your devices up-to-date. Downloading firmware updates from the manufacturer’s website will further enhance your router’s stability and performance. It will also help address potential security vulnerabilities if there are any. Remember, just like your PC or smartphone, your router also needs regular firmware updates to operate properly.
Avoid making online purchases whenever you’re in a public area (restaurant, coffee shop, shopping mall) and using their free Wi-Fi. There’s no way to ensure that the network is secure.
Using public Wi-Fi is riskier than a private home or work network. Here are some quick tips if you do use public Wi-Fi:
Shopping online typically means revealing your personal information that makes you vulnerable to identity theft and fraud. Things like your name, emails, social security number, and credit card information are all important nodes of your personal identity that must be encrypted and secured.
A VPN (virtual private network) creates a secure connection that protects your actual IP and encrypts your data. Using a VPN is easy, requires no extra hardware, and can be used from any device; desktop, laptop, mobile, tablet. For example, if you’re in New York and connect to a VPN location in Australia, websites will see you as a visitor from Australia.
The best part about a VPN is actually its encryption features. This means if you are browsing on a public Wi-Fi or Hotspot (coffee shop, airport, etc.), a VPN secures your core connection — allowing you to send your private information without worrying about the network being logged or recorded.

One of the first steps you should consider when setting up you browser security is cookies. Cookies are code snippets that allow websites to track your previous activity and display related and targeted information to you. This includes products, ads, logins and other user identifiable information. If you are ok with a less personalized experience, consider disabling cookies in your browser.
Here is how you do it in Chrome:
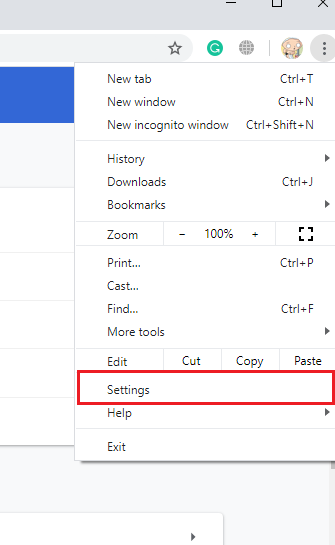
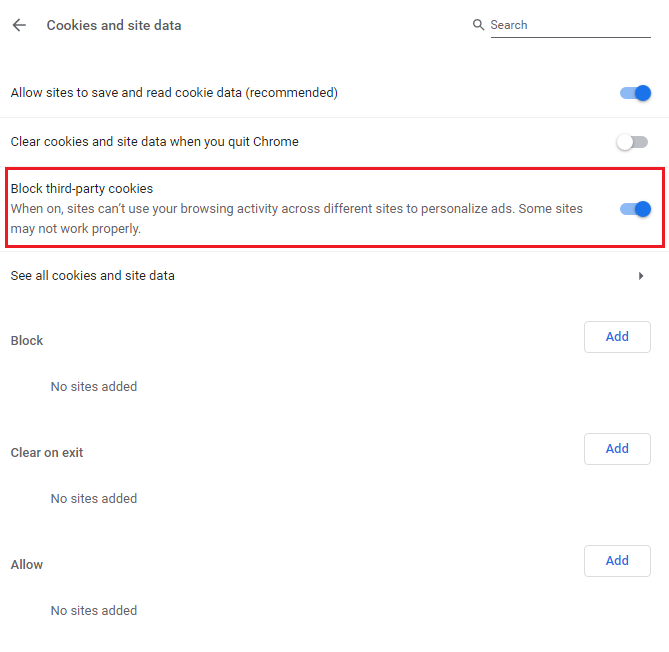
Check your browser settings on a regular basis. Configuring the privacy settings of your browser is the best way to ensure higher browser security. Browser settings, by default, leave your private data exposed. Here are some suggested settings:
Keep your browser cookies in check. Remove cookies after surfing the web (as shown above) and disable third-party access.
Disable redirects and pop-ups. Despite being annoying, redirects and pop-ups are often used to promote/spread malicious software.
Restrict access to your camera, microphone, and location. Set your web browser to ask for permission before it can access these features.
Deactivate ActiveX. It poses increased privacy and security risks. Deactivating ActiveX along with Flash are options you should consider disabling.
Here’s where you can find Privacy Settings on Chrome, Edge, Firefox, and Safari:
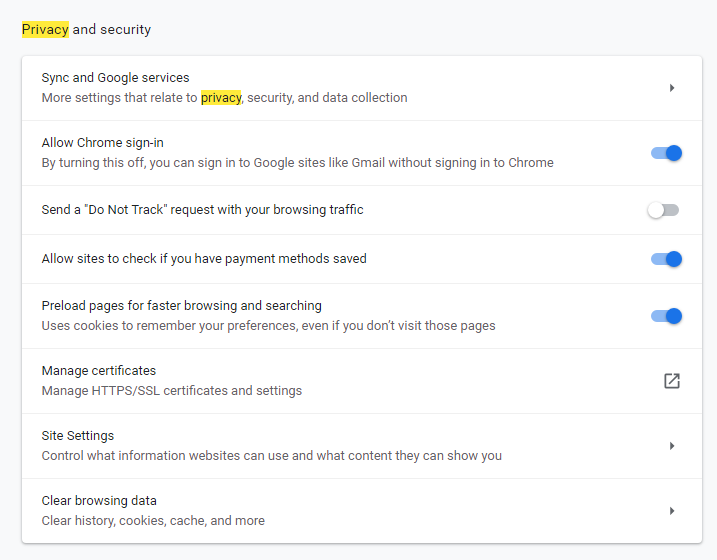
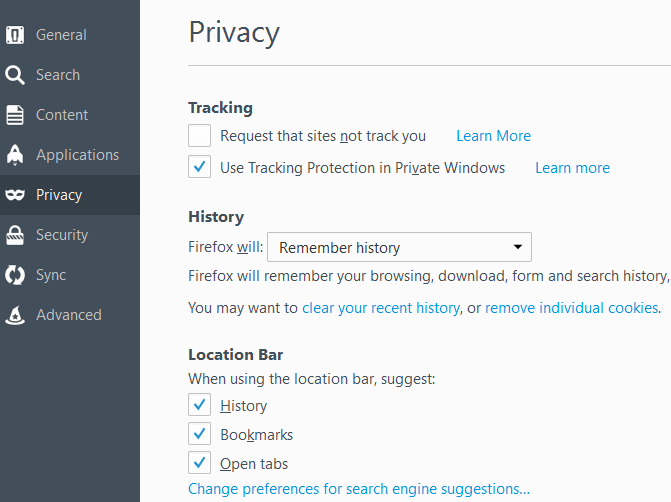
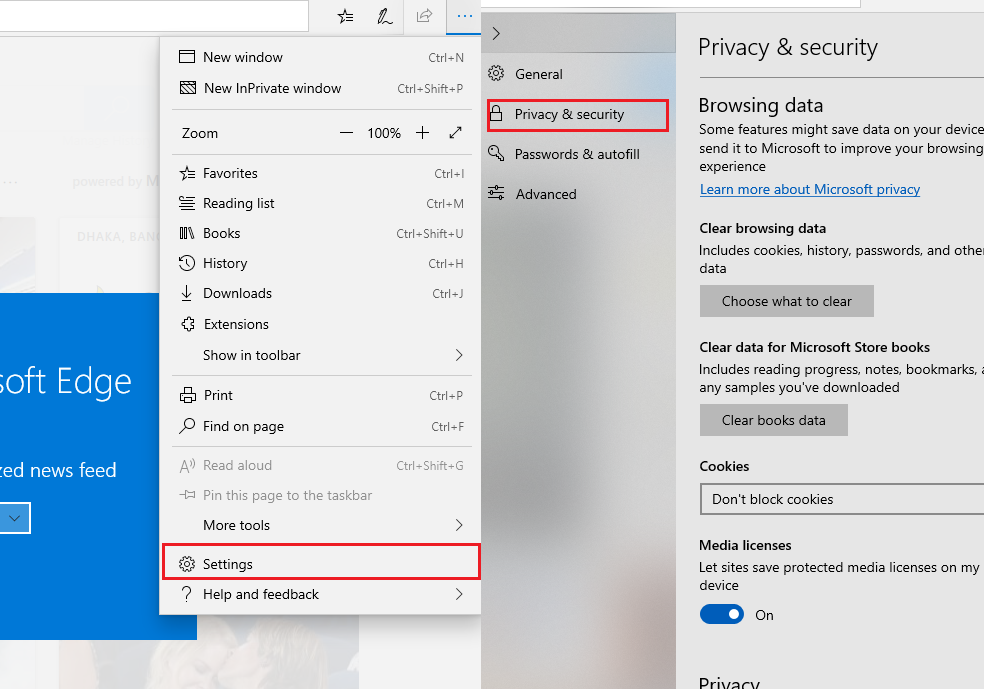
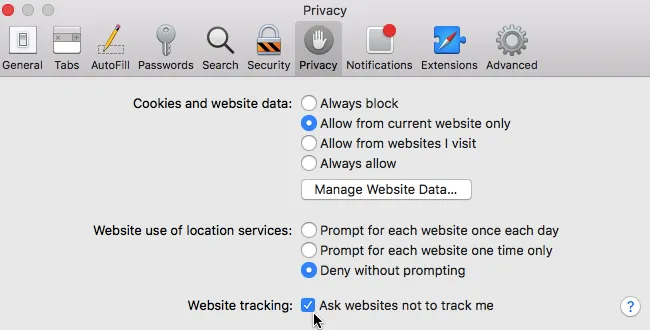
Take your time to understand the settings of your preferred browser and research more security tips online. You’ll be surprised to see there are countless loopholes that you never knew existed.
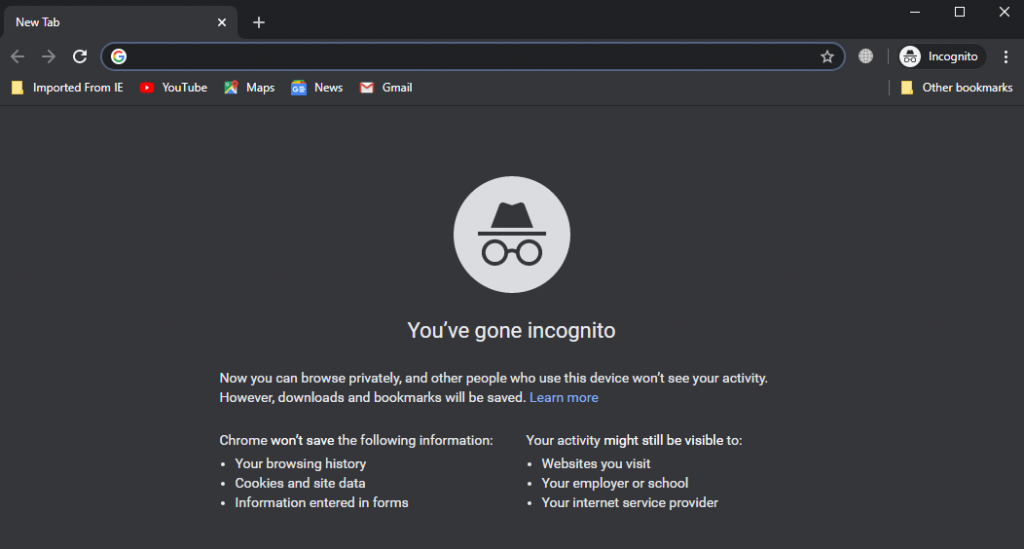
Browsing in a private window isn’t the ultimate privacy solution — your IP and activities are still visible— but it does prevent your browser from storing history, cookies and cache once you close the window.
Note: Simply minimizing or hiding the window won’t erase any data; Close the private window completely.
While it’s called Incognito Mode on Google Chrome, Edge calls it InPrivate Window and you can access it by pressing Ctrl+Shift+P. Firefox and Safari also have private browsing options available.
Most popular web browsers allow you to install security extensions to improve your browser’s privacy and security. When using an extension, you need to ensure it has been approved by Chrome or the browser developer that you are using. Also, don’t forget to enable automatic updates to keep your extensions up-to-date.
Here are a few recommendations to consider:
Many websites offer limited support for encryption over HTTPS. However, they don’t make it any easier to use. For example, they might default to unencrypted HTTP, or fill encrypted webpages with links that direct you back to the unencrypted pages. It rewrites unsecure requests to HTTPS.
Click & Clean is another free extension for Chrome widely used as a robust private data Cleaner. It's currently one of the top-rated extensions in the Chrome Web Store. Millions of home users and businesses are actively using this extension to protect their browsing history and other private information from third-parties.
Block ads that interrupt your browsing experience using Adblock Plus. With this extension, avoiding tracking and malware is effortless. Blocking intrusive ads lowers the risk of "malvertising" infections. Blocking tracking prevents organizations from following your online activity. It’s an open-source extension and is compatible with all major browsers.
uBlock Origin is an open-source, cross-platform browser extension for content-filtering, including ad-blocking. It’s easy on your CPU and memory footprint, and yet can load and enforce more filters than a lot of other browser extensions. uBlock Origin is available on all major web browsers, including Chrome, Chromium, Firefox, Edge, Opera, and Safari.
Disconnect blocks invisible tracker requests within your browser and applications while decreasing page load times. It is currently available for Firefox, Chrome, Opera, and Safari.
Blur secures all the personal information you put online — making it safe and easy to log-in and checkout from your browser, phone, or tablet. It’s cross-platform and works with all major browsers.
If your browser is not up-to-date, it won’t be able to fully protect you from new emerging security threats. When it is a question of software updates, each browser acts differently. Let’s see how updates are managed in Chrome, Firefox, and Safari.

An essential tip every consumer should consider is to look for encryption on all visited sites.
Secure websites depend on technology offered by a Secure Sockets Layer (SSL) certificate. It protects the information transmitted from the device to the website’s server. This secure encryption is generally indicated by a closed padlock symbol and “HTTPS” address bar.

Outside of SSL, you also need to pay attention to trust badges which add an additional layer of protection and authenticity for financial transactions.
Here are some of the trust badges you should look for:
Symantec offers enterprise-level strength SSL/TLS Certificates. It’s regarded as the world’s most advanced Certificate Authority, meaning all your transactions are secure.
eCommerce store owners use the “Verified & Secured” badge that comes with this SSLCertificate to ensure that all your sensitive information is secure.
Comodo SSL works as a safeguard and demonstrates that all data and communication transmitted through the websites are protected.
This is one of the most trusted “trust badges” on the Internet. GeoTrust Secured Seal indicates your information is protected.
The TrustLock verification badges indicate verified business, SSL secure, and better privacy for consumers.
If you come across a Truste certification seal, it means the website, app, or cloud platform is boasting higher privacy.
Most users purchase from a variety of different websites and usually reuse the same password for all their accounts which exposes them to extra risk. All it takes is one website breach for all your logins to be accessed by a third party.
We recommend using multiple passwords for all your login information. You should use 2FA on websites that store your PPI and financial information.
Using a password manager will help you manage multiple passwords and encrypt them. Some internet security software and antivirus programs include password security and management features.
Dashlane and LastPass are two password managers have had high ratings. They will simplify and secure your login process by helping you create more secure passwords and automatically log you in.
Here are some password setting tips for you to follow:
Policies such as the General Data Protection Regulation and California Consumer Privacy Act have enforced additional protection for consumers and their data. These policies are designed to ensure that consumer information that is being collected is disclosed and used in accordance with the law. However, there are still things you should consider and pay attention to when signing up on any website.
Every privacy policy has to disclose the type of information that is being collected. Avoid any service that collects multiple fields of Personally Identifiable Information unless it's a government website.
Websites will often collect your information either through a form input or cookies. The information they collect through cookies can also expose you to additional risk. We recommend following the cookie guidelines we outlined above to protect your data.
Websites must disclose how they intend to use the data that they collect. If the entity intends to use your data in additional ways, it must disclose this and provide an opt out feature.
A lot of sites share your information with third party companies and services. For example, Facebook sharing your data with advertisers to provide more relevant ads.
Even if a website is fully transparent about its data sharing practices and implements basic security standards such as SSL, look for websites that implement additional layers of data protection such as database encryption.
If a website collects information that is not required for essential user experience, this information should be optional. For example, an online retailer should not require a list of your hobbies to deliver a product your purchased.

With more than $581 billion dollars projected to be spent inside mobile apps in 2020, it’s no surprise that mobile applications have now become a major target of data breaches and cyber attacks. Many applications rely on private user information making them vulnerable to hackers, malware and other nefarious activity.
The base line for all mobile applications is data encryption. Once a user inputs personal information, that information must be encrypted and never stored or displayed in plain text anywhere within the application infrastructure.
When an application is compromised by malware, rogue apps or other cyber attacks, individuals face significant risks of digital fraud that includes:
Before you download and use any app, do your research on the company that developed it. The more information the developer has provided about itself, the less likely you are at a risk of downloading a rogue app. Some information that legitimate companies provide includes contact information, website, physical address, etc.
Here are some more important tips to ensure you’re not exposing yourself to additional risk:
Always download from App store hubs on Android or iOS. Never download mobile apps directly from third parties. All apps in designated app stores go through security checks.
Avoid apps that save passwords in their database or in the cloud. If an app requires a password to login, always manually enter into the input field and never save it.
Check that your app logs you out automatically after a short period of inactivity or idle behavior. Whenever possible, log out after using the app.
Anti malware software companies like Norton or McAfee offer mobile specific products that enhance security for your device. Consider getting one.
Permissions are critical component of any mobile app and the extent to which they have access to your device can actually be set by you. Keep in mind that disabling certain app permissions will render the app useless since certain permissions are at the core of App functionality. For example, TikTok not having access to your camera. Here are some essential app permission settings that you should consider.
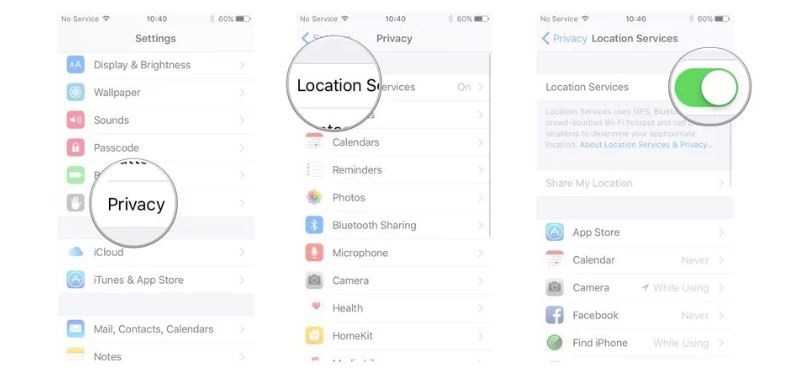
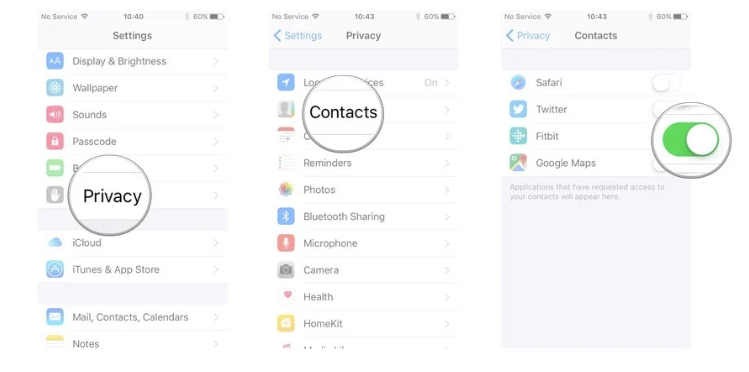
(Source)
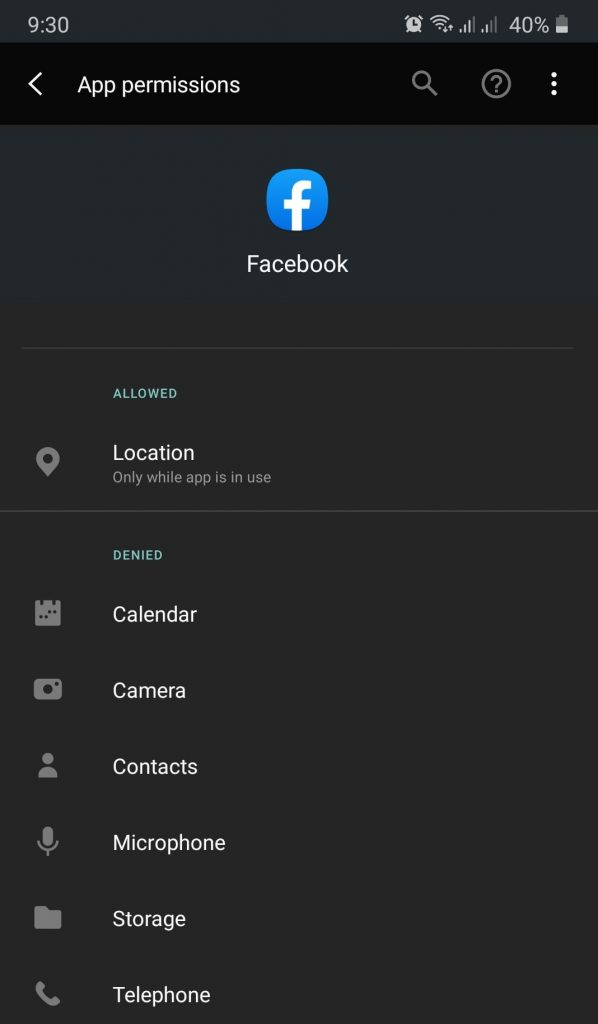
Now what you should allow or deny? It really depends, but the general rule of thumb is to deny all but necessary access for you to be able to use the App. For example, if you have a document scanning app, you might want to enable permission for Camera when using the app. Below we’ve outlined the risks and dangers associated with giving apps permissions to specific features.
Apps with this permission will be able to view all your messages including 2FA verification codes and send messages or sign up for services on your behalf.
Apps will be able to access your full calendar and see your past and future events. A lot of spyware target this feature.
Apps can take photos or record videos at any time. Exposes you to the risk of breached private images and videos.
Full access to your contact list including phone numbers, emails and other personal information. Used and abused by companies as well.
Allows for full tracking of owner location and exposes you to risk of home, work and other private address information leaks.
Gives full access to voice call functionalities including call logs, call termination and eavesdropping.
Allows for full access of all files stored on your device including photos, videos and documents.
Grants full access to recording all sound including calls, video calls and even conversations.

Using your credit card to purchase online is safer than using a debit card. If there’s a security breach, credit cards have consumer protection features that debit cards do not.
When it comes to credit cards, you need to be aware of the Address Verification Service (AVS), which is a robust first-line defense tool provided by bank issuers and card processors to merchants in order for them to detect fraudulent transactions.
When a consumer enters their address during checkout, AVS does the following:
AVS is used when a merchant verifies credit card data like billing address, ZIP code, etc. against the MasterCard/Visa billing information of the cardholder. It ensures that the credit card billing address matches the address given by the consumer.
Let’s check out the pros and cons of credit cards to determine what makes them a better option for online shopping.
You can set spending limits for your credit card, whereas a debit card linked directly to your bank account doesn’t allow it.
Money spent on an eCommerce site from your account via a debit card is far more difficult to recover as opposed to a credit card.
You can use your credit card with a low credit limit. Some banks even offer credit cards specially designed for e-shoppers, like ‘virtual or one-time-use credit cards.
You’re spending money that you don’t have yet. So, when not careful enough, this can often lead to unexpected debts.
Mismanaging a credit card not only leads to a high balance, but also to debts in the form of fees and interests.
Credit cards are easily stolen; numbers can be copied; they are often used to steal money or identity.
Third-party payment services like PayPal are also a great option for online shoppers. With PayPal, you don’t have to provide your bank account or credit card information to every eCommerce site you shop on. Instead, you keep that sensitive information with PayPal.
PayPal is fast, responsive, and easy to use. It works with almost every popular eCommerce site. As you make a purchase, PayPal processes the payment right away.
Google Pay is accepted at more places than people think. It works on most popular eCommerce stores and select supermarkets, restaurants, pharmacies, clothing stores, other retailers that accept mobile payments.
Once you set up your Google Pay account, you’ll be able to use it to make payments online. When you’re shopping in an app, look for a button at checkout that says “Buy with GPay.”
Square Wallet is a free app that lets you pay at hundreds of thousands of online and offline stores using your smartphone. Once you download the Square Wallet app from the Google Play or iTunes App Store, you’ll be asked to enter your credit card information and upload a real photo of yourself.
Most online and physical stores accept debit cards. If you’re paying for a product online, you can use your debit card just like a credit card. Note that you’re not as protected against fraud when using a debit card versus a credit card.
In order to pay with crypto (ie: Bitcoin, Litecoin, etc.), you must have a digital wallet — an app/software. These wallets are somewhat equivalent to having bank accounts.

Even if you have taken all the steps outlined above to protect yourself from cyber attacks, there is still a possibility that your data might be comprised due to no fault of your own. Companies get hacked and comprised even with enhanced levels of security. Look no further than Equifax and its debacle in 2017 when the data of 147 million consumers was breached and exposed. (Source) If a company which offers services that help protect consumers from fraud and identity theft can get breached, so can most other companies and services.
This is why Identity Theft Insurance should warrant your consideration. It is designed to cover expenses related to re-claiming your financial identity, repairing credit reports and nullifying unauthorized loans.
When it comes to identity theft insurance, there are three available options:
Depending on which policy you decide to go with, identity or fraud transactions insurance usually covers the following expenses:
Before you decide to get a stand alone policy, please speak with your current insurance provider as they typically offer discounted identity theft insurance for existing customers. Understand your policy limits, look for deductibles, and find out what limitations apply.
Identity monitoring and recovery services can help serve as an insurance measure that help you recognize identity theft early on and recover. These services will not protect you from fraud or identity theft, but they will mitigate the impact. Monitoring typically includes credit monitoring and identity monitoring which keeps track of the following:
There is a lot of identity and credit monitoring service on the market today and most of them offer similar perks and pricing. Just remember that they will not protect you against fraud or identity theft. There also free alternatives that you can use and we’ve listed them below:
You can get a free credit report on AnnualCreditReport.com which is the only authorized website for free credit reports. According to FTC you're allowed one free report every 4 months.
A credit/security freeze blocks all external access to your credit reports without your permission. This ensures that no-one can open new accounts in your name since creditors can't access your credit report. (Source)
Review all your bills and financial statements (debit, credit, etc.) every month to check for unrecognized charges.
Review explanation of benefits statements from health insurance providers and check for unrecognized treatments.
You are also eligible for one year free fraud alert on your credit report. This alerts the lenders and creditor to contact you and verify your identity before approving any new applications. You can renew the alert after one year for an annual premium.
Keep in mind that any credit freeze will restrict you from signing for services that require a credit check. You will have to manually lift the freeze by contacting a credit bureau so that the lender/provider is able to check your credit.
If you are a victim of identity theft or fraud, you will need to visit IdentityTheft.gov and report it first. This is a free federal government service that helps people report and recover from identity theft. They will:
This federal service has recovery plans for 30 different types of identity theft which even includes tax and child identity theft.
With Coronavirus forcing many Americans to stay and work from home, the current situation has undoubtedly increased the potential for cyber security fraud and theft. This is especially true for online purchases as many Americans have turned towards eCommerce to fill their needs. Credit card fraud is likely to eclipse 2019’s numbers by a significant amount as more people purchase products online and don’t implement the necessary data protection practices.
There is no 100% proof way to ensure that you are completely protected from data breaches, identity theft and fraud online. However, throughout this guide we outlined best ways to ensure that you minimize your risk whenever you do anything on the web. Taking these steps will significantly reduce your exposure to cyber threats and ensure your data and information is protected.
New fraudulent accounts pose the biggest financial risk to the American public and will most likely to continue in 2020 and beyond. (Source) If you are compromised and your information is obtained by nefarious third parties, monitoring and recovery steps outlined above will help you mitigate the impact.
But most importantly, protect your data at all cost and never reveal anything other than the minimum required information to purchase a product or subscribe to a service. Below you will find a list of other useful resources from government and non profit organizations.

Thanks for the guide! I did notice a few more covid-19 scams pop up in the last month (https://www.consumer.ftc.gov/blog/2020/04/scammers-are-using-covid-19-messages-scam-people). Bitcoin and webcam extortion scams are also have been a frequent and I’ve received quite a few in my inbox.